
Security in Cloud Computing
As you know "Cloud Computing" is recently one of the biggest trends of computer techs. Together with Cloud Computing especially data storage costs of companies go down sharply and at the same time their computational strength is incredibly rising. After some search thru many sources about Cloud Computing you will come to get this summary on Cloud Computing: it is the presentation of information technology (software, application, data storage, security, service etc) which is geographically based in one place or scattered around, via local networks or internet to the users. (Someone else can read the same definitions as a the pompously made and beautifully wrapped marketing of client/server architection to users, i.e., GNU founder Richard Stallman "It's stupidity. It's worse than stupidity: it's a marketing hype campaign," told The Guardian.)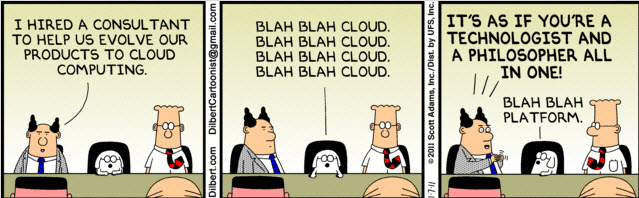
Cloud Computing is trend and of course it comes with some swanky terms. There is one acronym, an umbrella term for all aspects of IT to be delivered 'as a service' : XaaS (Everything as a Service) Today, nearly any type of hardware, software, IT or business process can be offered as a cloud-based service. This is creating an as-a-service economy that empowers both IT and the business. You can even say “I have a strong expertise in The Rolling Stones as a Service“ in a technical job interview to employer. I can assure you the person you talk won’t be reacted negatively. But anyway, before going into positive or negative parts of the Cloud Computing in terms of technical practise, I would like to mention to you shortly a few basic concepts that you should know about this matter. There are many kinds of service in cloud computing :
Software as a service (SaaS) means softwares, rather than being purchased, installed and maintenance-keeping, are more to be, thanks to a web browser, given to the users as a service based on internet. Examples are online word processing and spreadsheet tools (Google Docs) , CRM services and web content delivery services (Salesforce CRM).
Platform as a service (PaaS) allows users/customers to develop new applications using APIs deployed and configurable remotely. The platforms offered include development tools, configuration management, and deployment platforms. Examples are Heroku, Microsoft Azure, Force and Google App engine.
Infrastructure as service (IaaS) provides virtual machines and other abstracted hardware and operating systems which may be controlled through a service API. Examples include Amazon EC2 and S3, Terremark Enterprise Cloud, Windows Live Skydrive and Rackspace Cloud.
Data as a Service (DaaS) is a distribution model that data are made available to customers over a network.
Network as a Service (NaaS) offers network services virtually over the Internet. All these services can be on a pay-per-use or monthly subscription basis.
Believe me, we keep hearing new acronyms around cloud services every passing day.
A collection of overwhelming pros for Cloud Computing are very strong. It reduces your costs but increase your storage. It is paid incrementally (you pay only for what you need), saving organizations money in the short run. Money saved can be used for other important resources. Employees can access information wherever they are, rather than having to remain at their desks. Those seems fabulous but on the other hand we have two big issues : "Security" and "Reliance on 3rd Party". Are we sure there is a security standard? Are we in safe with the Control over own data is lost in the hands of an “difficult-to-trust” provider?
I strongly believe "Security for cloud-based data" will be the biggest concern in the near future. We have already heard a lot of news about this. For Example; classified documents detailing the data collection activities of the U.S. National Security Agency has been leaked 2013. (You really might want to check The Guardian - The NSA files) Or popular file-syncing service Dropbox just admitted to leaking an undisclosed number of user emails. I have a gut feeling that in the upcoming times, some problems will arise in the business layer and we will be seeing news about a lot of financially strong companies which will be about infiltration to their data.
Come to think of it, we are here talking about turning all your data, API keys, passwords and usernames over to the another 3rd party firm. This handing-over could be deliberately or totally non-deliberately and I frankly have never happened to see such a significant security protocol being made with any of our customers or companies I visited.
With an engineer overview into the cloud’s working logic, it’s highly possible to see “Encryption” shall be the new Religion of the Cloud. Encryption has gained a lot of attention Major service providers like Microsoft, Yahoo and Google set the tone by adding end-to-end encryption of data they host and manage for customers. For example, Google Cloud Storage now automatically encrypts all new data before it's written to disk. Microsoft has announced that it plans to ramp up encryption support for various services, including Outlook.com, Office 365, SkyDrive and Windows Azure.
By the end of 2014, Microsoft expects to have measures in place for encrypting data in transit between customer locations and its data centers, and while in transit between its own data centers. Like Google, Microsoft says it plans to encrypt all stored data in the cloud. Several other cloud services providers, like Dropbox, Sonic.net and SpiderOak, have announced support for similar data encryption programs, and for features like 2048-bit key lengths and the "Perfect Forward Secrecy" method for future-proofing encrypted data. (btw I am very intrigued with this Forbes news: Hackers, Here's a Way To Make An Easy $25k!)
In my opinion, brief controls you need to do with a corporate vision are as follows: To check how does technology architecture and infrastructure impact the cloud service provider’s ability to meet SLAs. To learn is encryption a software-only solution. (You need to know that it is possible to encrypt all the data at the hardware layer) Does they embrace ISO/IEC 27001 standard for information security management systems? To search “How long has the vendor been in business?", "What is their current financial standing?"
Considering the important aspects when it comes to personal use: if you want something done right, you should do it yourself. It would be best for you not to entrust your personal or sensitive data to any company before having them encrypted thru some programs such as BoxCryptor, TrueCrypt. While cloud providers may implement encryption, customers need to be aware that if providers hold encryption keys, it's still possible that they can access data -- or provide the keys to someone who requests them. In addition to all this, always choose two step verification. Always.
Remember, last thing you can do to protect your data is to put them on the internet. But if the price and performance costs are compelling you to use cloud solutions, it is better for you to be careful with these points.
Resources
- European Union Agency for Network and Information Security - Cloud Computing Benefits, risks and recommend: https://resilience.enisa.europa.eu/cloud-security-and-resilience/publications/cloud-computing-benefits-risks-and-recommendations-for-information-security
- Intel Cloud Security - Planning Guide: http://www.intel.com.tr/content/dam/www/public/us/en/documents/guides/cloud-computing-security-planning-guide2.pdf
Share this on → Tweet
